If you followed the steps of our Getting started with Boomi and Solace tutorial or have played around with the Solace PubSub+ Connector in your Boomi account, I hope you’ve found it pretty easy to connect, produce, and consume events using the PubSub+ Cloud service. This articles assumes that’s the case, so if you haven’t please go read/try those things and I’ll see you in a bit!
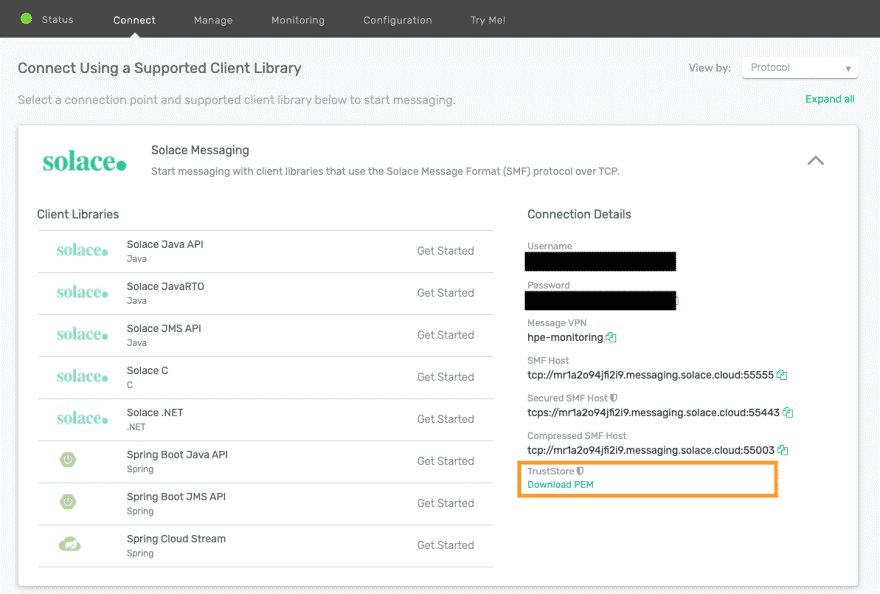
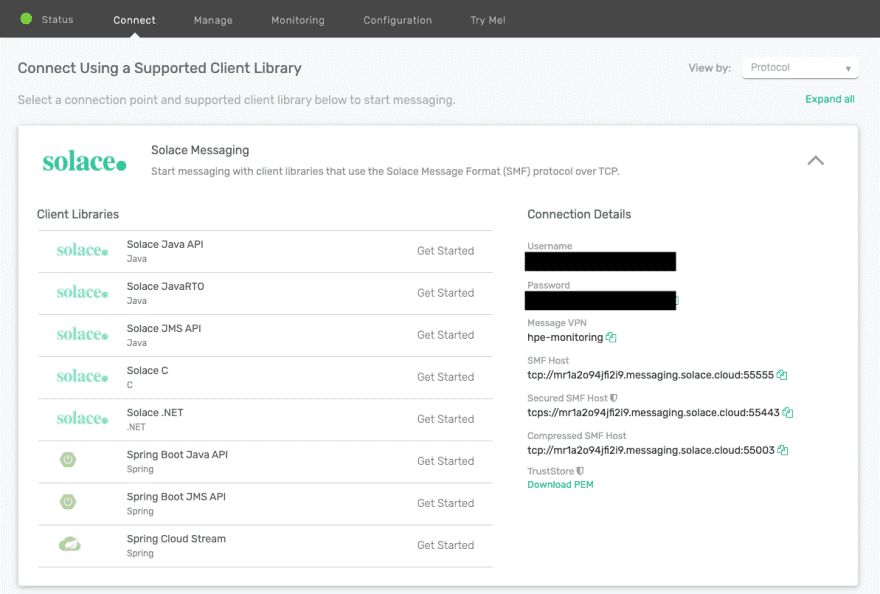
You probably noticed in the tutorial that you used a plain TCP socket to connect to PubSub+, and may have thought: “Wouldn’t it be better to use TLS encryption?” You may have even noticed in PubSub+ Service in PubSub+ Cloud a TLS-encrypted endpoint labelled “Secured SMF Host”. This should be easy — just use the secure endpoint and you’re done, right?
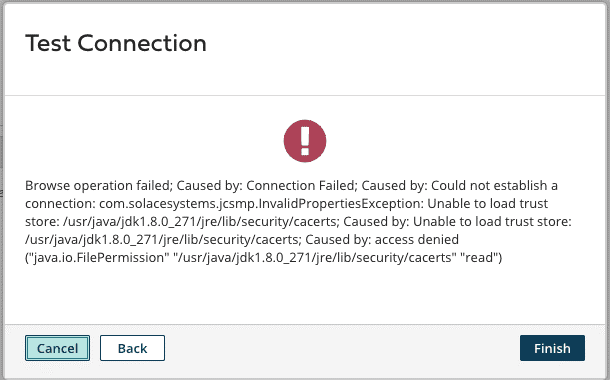
Unfortunately, it’s not. If you replaced the plain TCP connection URL with the secured URL (as I did in the screenshot below), then you tested the connection again using the handy “Test Connection” button in the Boomi Connection Setup dialog. Looks good…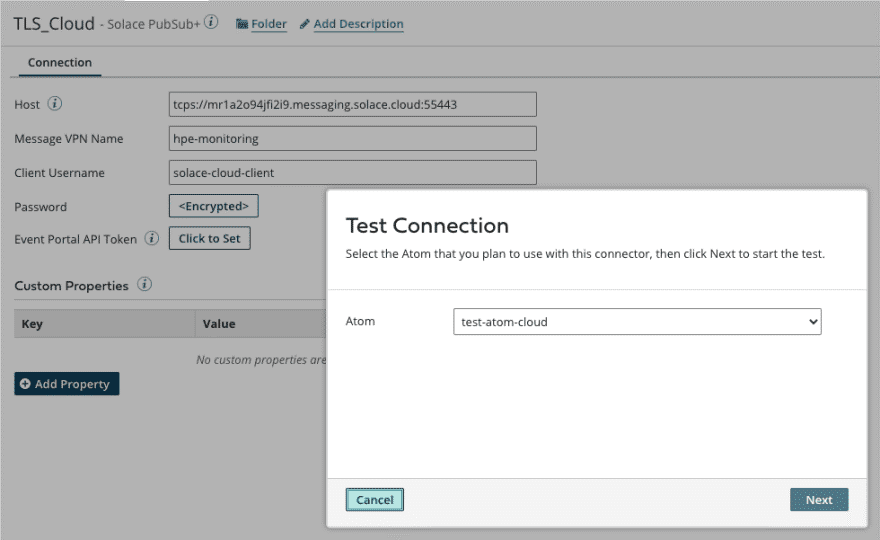
…unless you’re using a cloud-hosted Atom!
As you can see, the Connector tries to use the default Java trust store so it can verify the certificate presented by the PubSub+ service. And (for good reason) this access isn’t allowed in the cloud. Here’ how to get around that:
- Obtain or create a suitable trust store.
- Make the trust store available on the Atom.
- Tell the connector to use it.
Let’s look at each these steps.
Step 1: Obtain a Suitable Trust Store
PubSub+ Cloud services use a certificate signed by Digicert. The standard Java trust store includes the Root CA certificate. You can do this the easy way, or you can do it the hard way.
I’m an “easy way” guy myself, so will explain that first. As you can see, the Connector attempts to use cacerts which is included in all Java installations. You probably already have a few copies on your computer, so do a search and grab one. If not, you can get one from the OpenJDK repository like this one.
If you wanted to spend the time and energy to create a trust store with only the Root CA required by the Connector to connect to PubSub+ Cloud, you can do things the hard way.
First, download the root certificate from the PubSub+ Cloud console in PEM format:
Java requires the trust store in a Java Keystore format. To create the trust store in the required format you can follow steps 1 to 6 in Converting PEM-format keys to JKS format. In the following screenshots I used the easy way, but if you choose to do it the hard way just replace cacerts with the name of your trust store.
Step 2: Uploading the Trust Store to Boomi Atom(s)
With a trust store in place, how do you deploy it to your Boomi environment?
Every Boomi process has access to multiple folders. From that list the work and the userlib location stood out to me. Any process can write into the work directory so that may be an option, but while it’s marked as permanent storage, it reads like it’s intended for temporary storage. The other folder – userlib – is used to store custom libraries. These are a way to add additional Java libraries to a Boomi environment. It goes through the same packaging, versioning, and deployment cycle as Boomi processes themselves. Sounds like a good way to manage the rollout of a trust store! Here’s how:
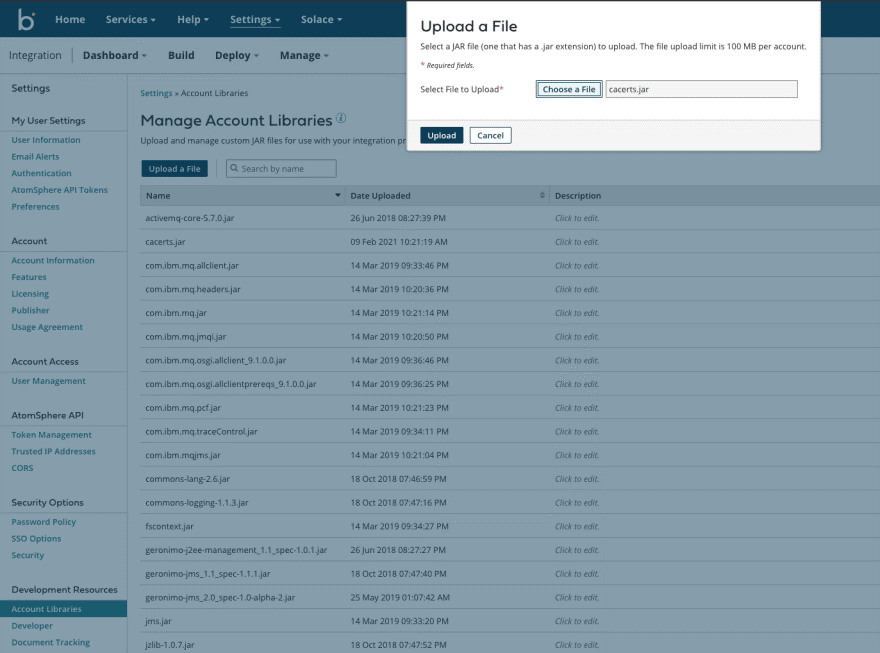
- Upload the trust store to the Account Library in your Boomi account.
- Create and deploy a Custom Library, and verify the trust store was uploaded to your Atom(s).
Here’s how you add the “Account Library”. Note that you are only allowed to upload JAR files, so you need to add .jar to your trust store’s file name. I have renamed mine to cacerts.jar.
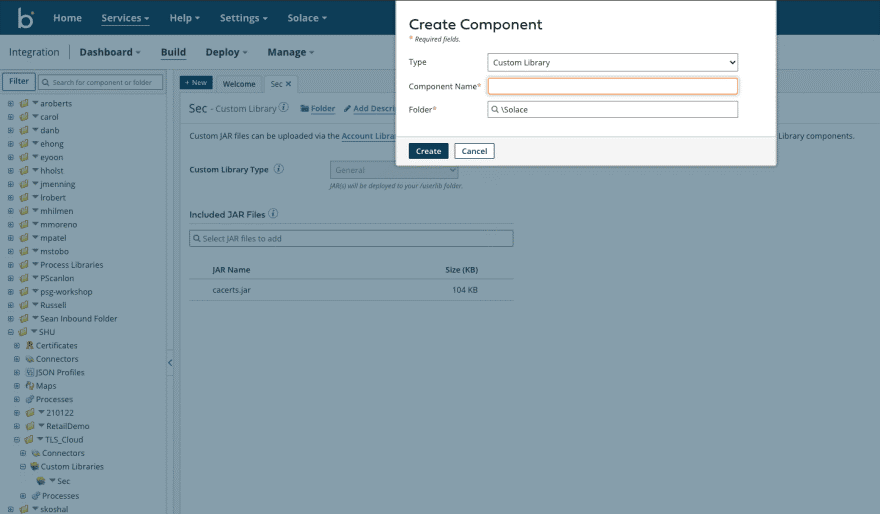
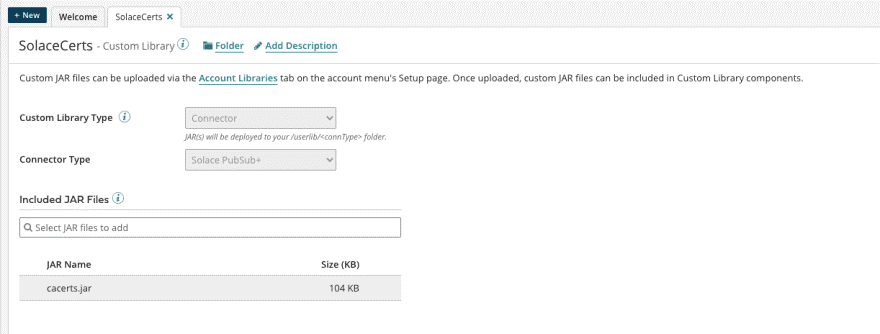
Then create the custom library like this. Note that the library I created is in the background, and how how I added the cacerts.jar.
If you prefer, when creating the custom library, you can choose to associate it with the connector by setting the library type to “connector” and connector type to “PubSub+ Connector”. This will put the trust store in a dedicated sub-directory of userlib.
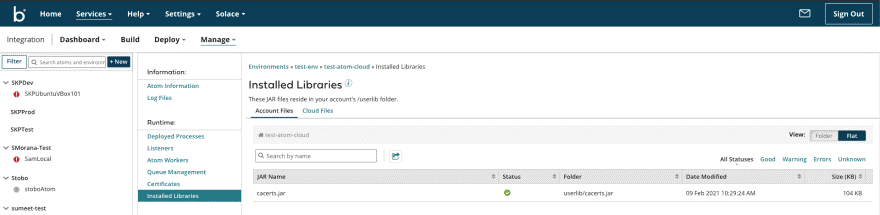
You then create a “Packaged Component” and deploy it to your environment. I’ll skip this here and fast-forward to the result when the library was applied to the Atom:
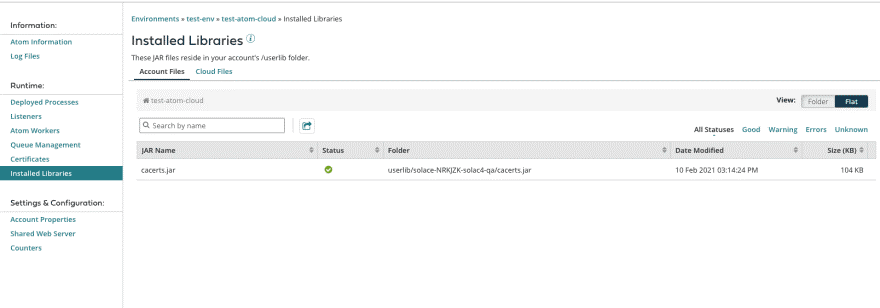
And here is what it looks like if you set the custom library type to “Connector”, note the sub directory that was created in userlib.
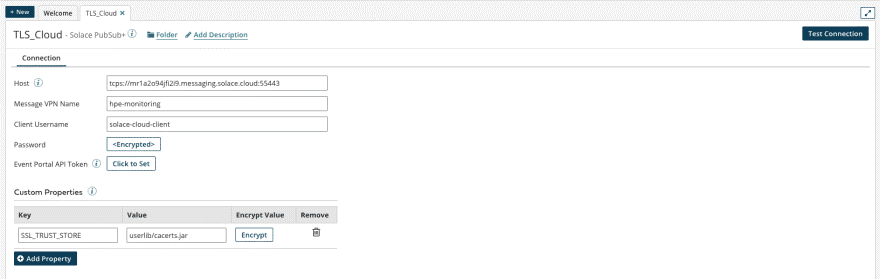
Step 3: Set Trust Store Used by the Connector
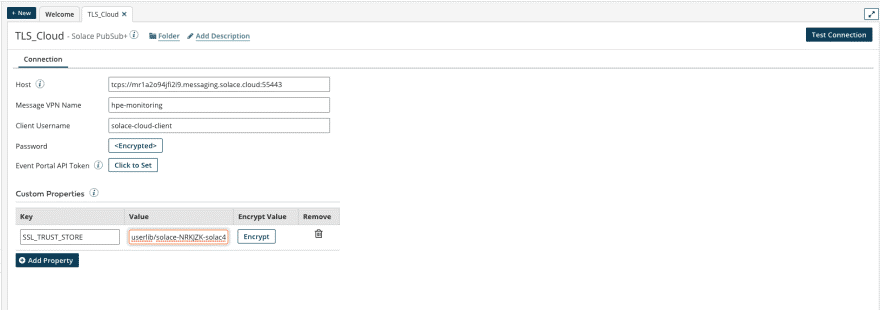
The last step is to let the connector know how to use the trust store. This is where the custom properties come into play. There is a property SSL_TRUST_STORE you can set and we point that to the file that was uploaded. Remember it’s in the userlib directory.
If you selected “Connector” as your custom library type, the trust store will be located in a subdirectory of userlib. You can look up the location in the Atom Management as seen in the screenshot of the preceding section.
There’s some information on these custom properties in the Connector’s documentation and a guide on the properties that you can use in the Solace API documentation.
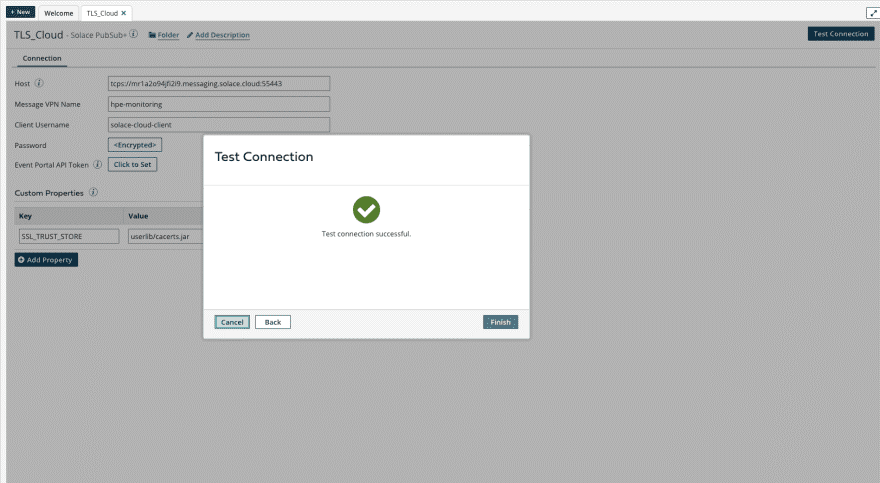
Now if you try “Test Connection” again and select an Atom in the environment you applied the custom library to, you should see a successful connection like this!
If so, congratulations! Whether you want to celebrate and discuss your accomplishment, or see what the community has to say about some difficulty you’re having, head over to our development community and join the conversation!
Explore other posts from category: For Developers

 Swen-Helge Huber
Swen-Helge Huber